The Ultimate Blockchain Engineering Interview Cheat Sheet: 25 Must-Know Questions
The Top Questions to Expect in an Interview
So you’ve landed an interview for a blockchain engineering position and you’re feeling pretty good about yourself. You’ve brushed up on your cryptography, you’ve spent hours tinkering with smart contracts, and you’re ready to dive into the world of decentralized applications and distributed ledgers. But then you start to think about the interview itself, and you start to feel a little anxious. What if they ask you a question that you can’t answer? What if you forget the difference between a hash function and a consensus algorithm?
I’ve compiled a list of the 25 most common questions you’re likely to be asked in a blockchain engineering interview, along with some helpful explanations and tips to get you through it. Whether you’re a seasoned blockchain veteran or a complete newcomer to the space, this list has something for everyone. So take a deep breath, relax, and let’s dive in!
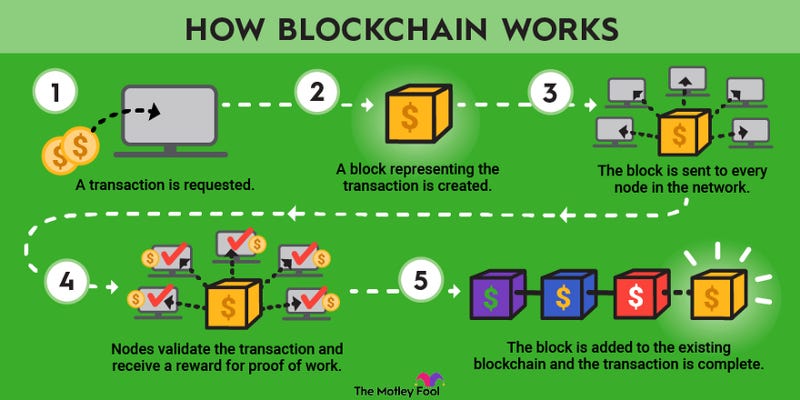
What is a blockchain and how does it work?
A blockchain is a digital, decentralized ledger that records transactions on multiple computers so that the record cannot be altered retroactively without the alteration of all subsequent blocks and the consensus of the network.
Here’s how it works:
When a transaction is made, it is broadcasted to a network of computers, called “nodes.”
These nodes validate the transaction and the user’s status as the owner of the asset being transferred.
Once a transaction is verified, it is combined with other transactions to create a new “block” of data.
This block is then added to the existing “chain” of blocks, which is just a record of all the blocks that have been created since the beginning of the blockchain.
The completed block is then added to the chain, which is stored across the network of computers.
This process is known as “mining.” Miners are nodes on the network that process transactions, and in return for their work, they are rewarded with cryptocurrency.
The main benefit of a blockchain is that it is secure and transparent. Because the transaction record is distributed across a network of computers, it is virtually impossible to hack or alter. Additionally, all transactions are recorded and can be viewed publicly, so it’s easy to see what has happened on the chain.
How does a block get added to the blockchain?
a block is added to the blockchain through a process called mining. Here’s a high-level overview of how it works:
First, someone (a miner) needs to create a new block that they want to add to the blockchain. This block typically contains a list of transactions that have occurred since the last block was added to the blockchain.
The miner then performs a complex mathematical calculation (also known as a “proof of work”) to find a special number, called a “nonce.” This nonce, when combined with the transactions in the block and a few other pieces of data, results in a unique code called a “hash.”
The miner then submits the new block, along with the nonce and the hash, to the rest of the network for verification.
Other miners on the network will then check to make sure that the transactions in the block are valid and that the hash is correct. If everything checks out, the block is considered to be “mined,” and it is added to the blockchain.
Once the block is added to the blockchain, it becomes a permanent part of the distributed ledger, and the transactions it contains are considered to be complete.
The process then starts over, with a new block being created and added to the blockchain.
In a nutshell, a node collects some transactions from the network, and after that it combines those transactions with some information from previous block, nonce, and its own info and creates a hash. If the hash is valid, then the node can create a block and sends it to the rest of network for validation. If the hash is not valid, it will use another nonce until it finds a valid hash. So, the next question is what is a valid hash? This will be answered later.
How does the blockchain ensure that a transaction is valid?
There are a few different ways that the blockchain helps to ensure that transactions are valid. First and foremost, it uses a system of cryptography to verify the authenticity of each transaction. This involves the use of digital signatures, which are unique codes that are generated by the sender of the transaction. These signatures serve as a kind of “digital fingerprint” that can be used to verify the identity of the sender and ensure that the transaction is coming from a trusted source.
Another way that the blockchain helps to ensure the validity of transactions is through the use of a distributed ledger. This is essentially a database that is spread out across a network of computers, rather than being stored in a single central location. This means that there is no single point of failure, and it is much harder for someone to tamper with the ledger or make fraudulent transactions. So, if a transaction is not valid, you might fool a few blocks, but it’s impossible to pass through hundreds of them.
Finally, the blockchain uses a system called “consensus” to verify the validity of transactions. Essentially, this means that all of the computers in the network must agree on the validity of a transaction before it can be added to the blockchain. This helps to prevent fraud and ensures that only legitimate transactions are added to the ledger.
Overall, the combination of cryptography, a distributed ledger, and consensus make the blockchain a very secure and reliable way to verify transactions.
What is a consensus algorithm and how does it work?
A consensus algorithm is a way for a group of computers to come to agreement on the current state of a distributed system, such as a blockchain. The goal of a consensus algorithm is to allow the computers in the system to agree on a single version of the truth, even in the presence of malicious actors or faulty hardware.
There are many different types of consensus algorithms, but they all work by allowing the computers in the system to “vote” on the validity of a particular transaction or set of transactions. The specific process for doing this can vary, but here is a general overview of how it works:
A transaction is proposed and broadcast to the network.
The computers in the network, called “nodes,” validate the transaction to make sure it is valid and follows the rules of the system.
If a majority of the nodes agree that the transaction is valid, they will “vote” to approve it. This vote is usually in the form of a cryptographic signature.
Once a sufficient number of votes have been cast, the transaction is considered to be approved and is added to the distributed ledger.
The key advantage of a consensus algorithm is that it allows a distributed system to come to agreement without the need for a central authority. This makes it possible for the system to be decentralized, which can be more secure and resistant to tampering.
Here I give you top 5 commonly debated consensus algorithms in the world of blockchain:
Proof-of-Work (PoW) — This is the most widely used consensus algorithm in blockchain technology. It involves miners competing to solve complex mathematical puzzles in order to create new blocks and earn rewards.
Proof-of-Stake (PoS) — In a PoS system, validators put up a stake of their own cryptocurrency as collateral, and are then chosen to create the next block in the chain based on the size of their stake.
Delegated Proof-of-Stake (DPoS) — In a DPoS system, the network participants (also known as “delegates”) are chosen to create new blocks based on the number of votes they receive from other network participants.
Proof-of-Importance (PoI) — In a PoI system, the validators are chosen based on a combination of their stake and their “importance” in the network, which is often determined by factors such as the number of transactions they have processed or the amount of cryptocurrency they hold.
Proof-of-Authority (PoA) — In a PoA system, the validators are chosen based on their reputation and trustworthiness, rather than their stake or computational power. This is often used in consortium or private blockchains where the participants are known and trusted entities.
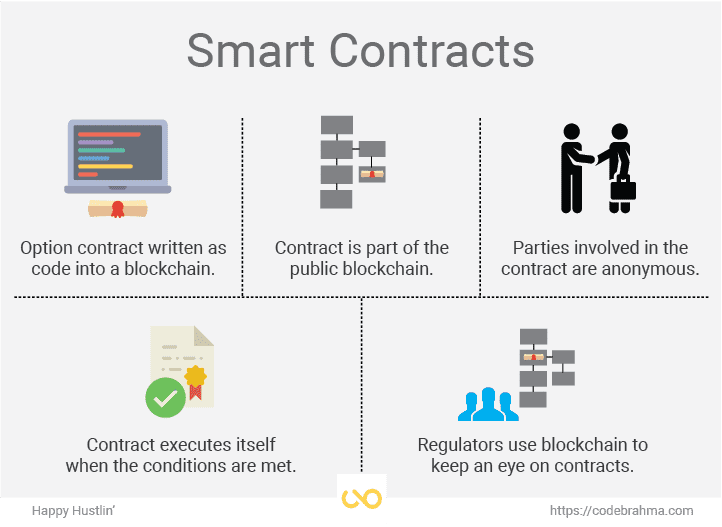
What is a smart contract and how is it used in blockchain?
A smart contract is a self-executing contract with the terms of the agreement between buyer and seller being directly written into lines of code. The code and the agreements contained therein exist on the blockchain network.
Smart contracts allow you to exchange money, property, shares, or anything of value in a transparent, conflict-free way while avoiding the services of a middleman.
Here’s how it works:
A smart contract is written with the terms of the agreement between two parties.
The contract is deployed on the blockchain and is now stored and replicated on the network.
The parties involved in the contract can now interact with the contract and execute the agreed-upon terms.
Once the terms of the contract have been met, the contract automatically executes and completes.
Smart contracts are often used to facilitate, verify, and enforce the negotiation or performance of a contract. They can be used in a wide range of applications, such as supply chain management, real estate, and financial services.
One of the key benefits of smart contracts is that they can help to eliminate the need for intermediaries, which can save time and money. They are also transparent and secure, since they are stored on the blockchain and can’t be altered once they have been executed. Here’s a simple example of a smart contract:
Alice and Bob are entering into a contract for the sale of a used car. They agree on a price of $5,000 and decide to use a smart contract to facilitate the transaction.
The smart contract is written with the following terms:
Alice will transfer ownership of the car to Bob upon receipt of $5,000.
Bob will send $5,000 to Alice upon receipt of the car.
The contract is then deployed on the blockchain and is now stored and replicated on the network.
When the time comes to complete the transaction, Bob sends $5,000 to the smart contract. Once the contract confirms that it has received the payment, it automatically transfers ownership of the car to Bob. At the same time, the contract releases the $5,000 to Alice.
In this example, the smart contract acts as a secure and transparent way to facilitate the transaction and ensure that both parties fulfill their obligations.
You can write this contract in the programming languages of your blockchain. For example, Ethereum blockchain uses Solidity. Let me give you a sample code of a smart contract in Solidity.
pragma solidity ^0.5.0;
contract SimpleContract {
// Declare a public variable
uint public value;
// Constructor function to set the initial value of the contract
constructor(uint initialValue) public {
value = initialValue;
}
// Function to increase the value of the contract
function increaseValue(uint _value) public {
value += _value;
}
// Function to decrease the value of the contract
function decreaseValue(uint _value) public {
value -= _value;
}
}This contract has three functions: a constructor function to set the initial value of the contract, a function to increase the value, and a function to decrease the value. Users can interact with the contract by calling these functions and passing in the appropriate arguments. For example, to increase the value by 10, a user could send a transaction calling the increaseValue() function with the argument 10.
Keep in mind that this is a very basic example, and real-world smart contracts can be much more complex and include a wide range of logic and conditions.
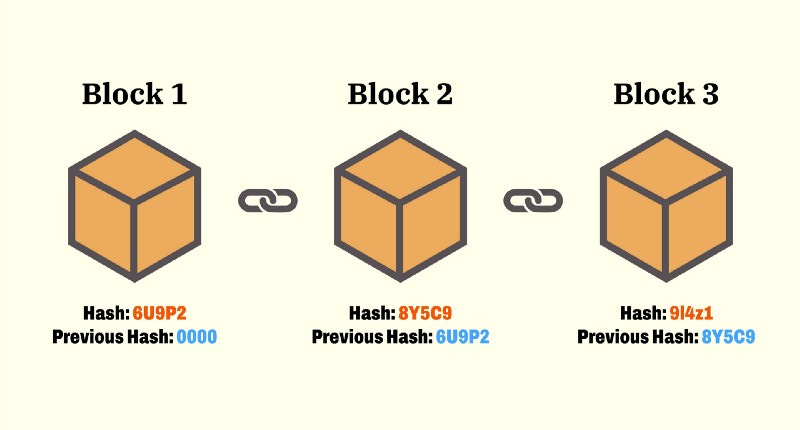
What is a hash function and how is it used in the blockchain?
A hash function is a mathematical function that takes an input (or “message”) and returns a fixed-size string of characters, which is known as a “hash.” The same input will always produce the same hash, but even the slightest change to the input will produce a completely different hash.
Hash functions are used in many different applications, but they are particularly important in the blockchain. In the context of a blockchain, a hash function is used to create a unique “fingerprint” for each block of transactions.
Here’s how it works:
A block of transactions is created.
The block is fed into a hash function, along with some other data (such as a nonce, which is a number that is used only once).
The hash function processes the data and produces a unique hash for the block.
The completed block, along with its hash, is added to the blockchain.
The hash serves as a sort of digital signature for the block, and it is used to confirm the integrity of the block and its contents.
One of the key benefits of hash functions is that they are one-way, which means that it is virtually impossible to determine the input (i.e., the original message) from the output (i.e., the hash). This makes them useful for protecting sensitive data, such as passwords.
In the context of the blockchain, hash functions are used to ensure the integrity of the data on the chain. If a malicious actor tries to alter a block, the hash for that block will change, which will be detected by the other nodes on the network. This helps to prevent tampering and ensures the security of the blockchain.
What are some of the popular programming languages in blockchain?
There are several programming languages that are widely used in the blockchain world, including:
Solidity — This is a high-level, object-oriented programming language that is specifically designed for building smart contracts on the Ethereum platform.
Vyper — This is a python-based language that is focused on simplicity and security, and is often used as an alternative to Solidity on the Ethereum platform.
Simplicity — This is a low-level, functional programming language that is designed for use in smart contracts and other blockchain applications.
C++ — This is a general-purpose programming language that is widely used in the development of blockchain software and applications, including cryptocurrency wallets and mining software.
Java — This is another general-purpose programming language that is commonly used in the development of blockchain-based applications and services.
Go — This is a programming language developed by Google that is often used in the development of blockchain software and applications, including the popular Ethereum software client, Geth.
Overall, the choice of programming language will depend on the specific needs and requirements of the project, as well as the preferences of the developers.
What are the steps you need to take to create your own blockchain?
To create a blockchain, you will need to:
Determine the purpose and goals of your blockchain: The first step in creating a blockchain is to determine what you want it to be used for and what you want it to achieve. This will help you decide on the key features and functions that your blockchain will need to have.
Choose a consensus algorithm: A consensus algorithm is the way that the blockchain network reaches agreement on the state of the ledger and the validity of transactions. There are several different consensus algorithms to choose from, including proof-of-work (PoW), proof-of-stake (PoS), and delegated proof-of-stake (DPoS).
Design the blockchain architecture: The next step is to design the overall architecture of your blockchain, including the data structures, cryptographic functions, and other technical details. You will also need to decide on the programming language(s) that you will use to build your blockchain.
Implement the blockchain: Once you have designed your blockchain, you can begin implementing it using your chosen programming language(s). This will involve writing the code for the various features and functions of your blockchain, as well as testing and debugging it to ensure it is accurate and error-free.
Deploy the blockchain: Once your blockchain is implemented, you will need to deploy it to the network. This typically involves setting up the necessary infrastructure (e.g., servers, storage, etc.), and inviting other users to join and start using the blockchain.
Below, I will give you a simple example code of a blockchain in Python:
import hashlib
import time
class Block:
def __init__(self, data, previous_hash):
self.timestamp = time.time()
self.data = data
self.previous_hash = previous_hash
self.hash = self.calc_hash()
def calc_hash(self):
sha = hashlib.sha256()
hash_str = f"{self.data}{self.timestamp}{self.previous_hash}"
sha.update(hash_str.encode('utf-8'))
return sha.hexdigest()
class Blockchain:
def __init__(self):
self.blocks = [self.get_genesis_block()]
def get_genesis_block(self):
return Block("Genesis Block", "0")
def add_block(self, data):
previous_hash = self.blocks[-1].hash
new_block = Block(data, previous_hash)
self.blocks.append(new_block)
blockchain = Blockchain()
blockchain.add_block("Data for block 2")
blockchain.add_block("Data for block 3")
for block in blockchain.blocks:
print(f"Data: {block.data}")
print(f"Timestamp: {block.timestamp}")
print(f"SHA-256 hash: {block.hash}")
print("\n")This code defines a Block class and a Blockchain class. The Block class has three attributes: data, timestamp, and previous_hash. It also has a calc_hash method that calculates the SHA-256 hash of the block. The Blockchain class has a list of blocks and has methods for adding blocks to the chain and generating the first block (called the "genesis block").
What are different blockchain architectures?
There are a few different blockchain architectures out there that you might want to know about!
Public blockchains: These are the most well-known type of blockchain, and they’re usually decentralized networks that anyone can join and participate in. Some examples of public blockchains include Bitcoin and Ethereum.
Private blockchains: These are blockchains that are typically used by organizations or groups and require permission to join. They can be used to create a secure, decentralized network for a specific purpose, like supply chain management or voting systems.
Consortium blockchains: These are a hybrid of public and private blockchains, where a group of organizations work together to create and maintain the network.
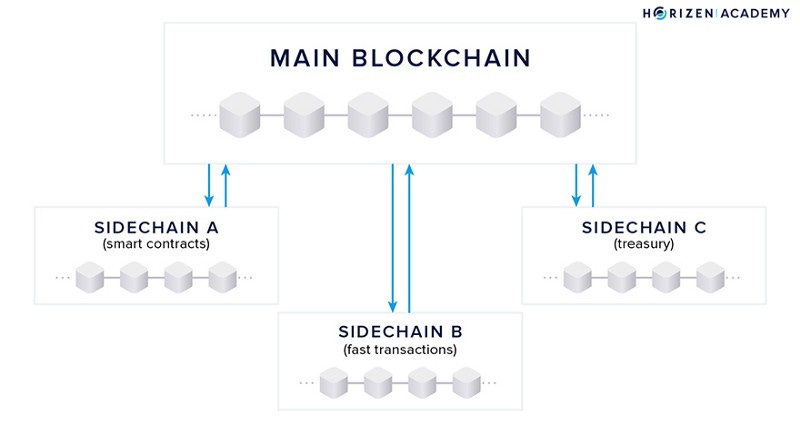
Sidechains: These are blockchains that are connected to a main blockchain, but operate independently and can be used for specific purposes or transactions.
Hybrid blockchains: These are blockchains that combine elements from both public and private networks, allowing for a mix of decentralized and centralized control.
What are the steps you need to take to deploy a blockchain?
Here are some steps you can follow to deploy your very own blockchain:
First and foremost, you’ll need to design your blockchain’s architecture. This will involve deciding on the type of consensus algorithm you want to use, the number of nodes you want to have in your network, and any additional features or functionalities you want your blockchain to have.
Next, you’ll need to implement your blockchain. This can be done using a programming language like C++, Python, or Go. You can also use a framework like Hyperledger Fabric or Ethereum to streamline the development process.
Once your blockchain is implemented, it’s time to set up your nodes. This will involve installing the necessary software on each of your nodes and configuring them to communicate with one another.
Now it’s time to test your blockchain to make sure everything is working as expected. This can be done using a variety of testing tools and techniques, such as unit tests, integration tests, and functional tests.
When you’re satisfied with the results of your testing, it’s time to deploy your blockchain to the public. This will involve setting up a network of nodes that are accessible over the internet and inviting other users to join your network.
Finally, you’ll need to maintain and monitor your blockchain to ensure that it continues to function as intended. This will involve keeping your nodes up to date with the latest software, handling any security issues that may arise, and monitoring the overall health of your network.
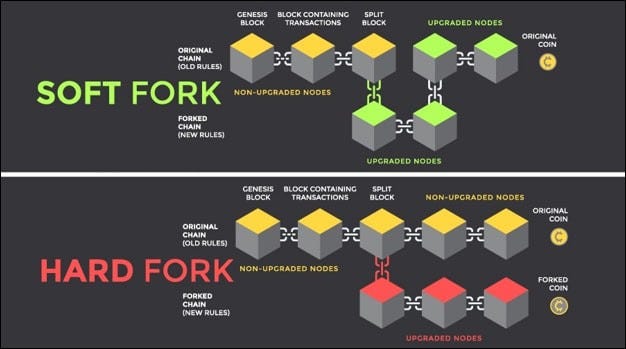
What is a blockchain fork and how does it occur?
A blockchain fork occurs when a blockchain splits into two separate chains. This can happen for a number of reasons, but the most common reason is a change in the rules that govern the blockchain.
Here’s how it works:
A group of users (or “miners”) proposes a change to the rules of the blockchain. This could be a change to the way transactions are processed, the way the network is secured, or any other aspect of the blockchain’s operation.
The proposed change is broadcast to the network, and users can choose whether to accept or reject the change.
If a majority of users accept the change, the blockchain is “forked,” and the new rules are implemented.
If a minority of users accept the change, the blockchain will continue to operate under the old rules, and a new, separate blockchain will be created for the users who have adopted the new rules.
There are two main types of forks: hard forks and soft forks.
A hard fork is a permanent split in the blockchain, and it creates a new, separate blockchain with its own set of rules. This means that users who do not adopt the new rules will no longer be able to participate in the blockchain.
A soft fork, on the other hand, is a temporary split in the blockchain, and it does not create a new, separate blockchain. Instead, the old and new versions of the blockchain are compatible, and users who do not adopt the new rules can still participate in the blockchain.
What is a mining node and what is its role in the blockchain?
A mining node is a computer that participates in the process of validating transactions and adding them to a blockchain. The term “mining” refers to the process of producing a valid hash for a new block of transactions, which is a computationally intensive task.
In return for their work, mining nodes are rewarded with cryptocurrency. This is how new tokens are introduced into the system and how miners are compensated for their work.
Here’s how mining nodes work in the context of a blockchain:
A transaction is broadcast to the network.
Mining nodes on the network receive the transaction and validate it to make sure it is valid and follows the rules of the system.
Once a transaction has been validated, it is combined with other transactions to create a new block of data.
The mining nodes then compete to produce a valid hash for the block. This involves using a hash function to process the data in the block and producing a unique hash that meets certain criteria (such as being unique and difficult to produce).
Once a valid hash is produced, the block is added to the blockchain and the transaction is complete.
Mining nodes play a crucial role in the blockchain by helping to validate transactions and keep the network secure. They ensure the integrity of the blockchain by making it difficult for malicious actors to alter the data on the chain.
In terms of validation, it’s important to know how these nodes validate transactions. When a mining node receives a new transaction, it performs a series of checks to validate the transaction and make sure it is valid and follows the rules of the system. Here are some examples of checks that a mining node might perform:
Check the transaction format: The mining node will verify that the transaction is properly formatted and follows the rules for transactions on the particular blockchain.
Check the user’s status as the owner of the asset: The mining node will verify that the user has the right to transfer the asset (e.g., by checking the user’s cryptographic signature).
Check the transaction against the current state of the blockchain: The mining node will verify that the transaction is consistent with the current state of the blockchain (e.g., by checking that the user has sufficient funds to complete the transaction).
If the transaction passes these checks, the mining node will “vote” to approve it and will include it in the block of transactions that it is currently working on.
What is a decentralized application (DApp) and how does it differ from a traditional application?
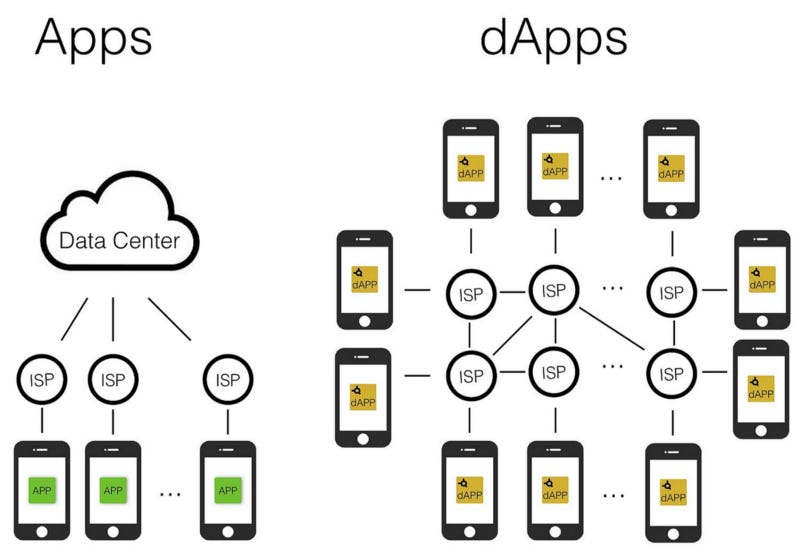
A decentralized application (DApp) is a software application that is built on top of a decentralized platform, such as a blockchain.
One of the key differences between a DApp and a traditional application is that a DApp is decentralized, meaning that it is not controlled by a single entity or organization. This makes it more resistant to censorship and tampering, and it allows for the creation of applications that are more transparent and secure.
Another difference is that DApps are often open source, which means that the source code is publicly available and can be reviewed by anyone. This can help to ensure the integrity and security of the application.
Here are some other key differences between DApps and traditional applications:
Architecture: Traditional applications are usually built on a client-server model, where a central server stores and processes data. DApps, on the other hand, are built on a peer-to-peer model, where data is stored and processed on multiple nodes in the network.
Data storage: Traditional applications usually store data in a centralized database, while DApps store data on a decentralized database, such as a blockchain.
Consensus mechanism: DApps often use a consensus mechanism, such as proof of work or proof of stake, to reach agreement on the state of the application and the validity of transactions. Traditional applications do not use a consensus mechanism.
Here is a list of five popular decentralized applications (dApps):
CryptoKitties: a game that allows users to buy, sell, and breed virtual cats using cryptocurrency.
Augur: a decentralized prediction market platform that allows users to create and place bets on the outcomes of real-world events.
Ethlance: a freelance job market platform built on the Ethereum blockchain.
Golem: a decentralized platform for sharing computing power, allowing users to rent out their excess CPU and GPU capacity.
0x: an open protocol that allows for the creation of decentralized exchanges (DEXs) on the Ethereum blockchain.
What is a distributed ledger and how does it differ from a centralized ledger?
A distributed ledger is a type of database that is stored and replicated across a network of computers, rather than being stored in a single location. Each copy of the ledger is constantly updated and validated to ensure that it is consistent with all of the other copies on the network.
One of the key features of a distributed ledger is that it is decentralized, which means that it is not controlled by any single authority. Instead, it is maintained by a network of computers, which work together to validate and record transactions.
A centralized ledger, on the other hand, is a database that is controlled by a single authority and stored in a single location. This means that all transactions must go through the central authority, which acts as a gatekeeper for the ledger.
There are a few key differences between distributed and centralized ledgers:
Decentralization: As mentioned above, a distributed ledger is decentralized, while a centralized ledger is controlled by a single authority.
Security: A distributed ledger is generally considered to be more secure than a centralized ledger, because it is more difficult for a single entity to alter the data on the ledger.
Transparency: A distributed ledger is typically more transparent than a centralized ledger, because all of the copies of the ledger are constantly being validated and updated.
What is a digital signature and how is it used in the blockchain?
A digital signature is a way to verify the authenticity of a message or document, and it is often used to secure communications and transactions on the internet. In the context of the blockchain, a digital signature is used to verify the identity of the sender of a transaction and to ensure that the transaction has not been tampered with.
Here’s how a digital signature works:
A message or document is created.
The sender uses a private key to create a digital signature for the message. The private key is a secret code that only the sender knows.
The message and the digital signature are sent to the recipient.
The recipient uses the sender’s public key to verify the digital signature. The public key is a code that is publicly available and can be used to verify the signature.
If the digital signature is valid, the recipient can be confident that the message is authentic and has not been altered.
Digital signatures are an important part of many blockchain systems, as they provide a way to verify the identity of the sender of a transaction and to ensure that the transaction has not been tampered with. They are a key component of the security of the blockchain, and they help to prevent fraud and abuse.
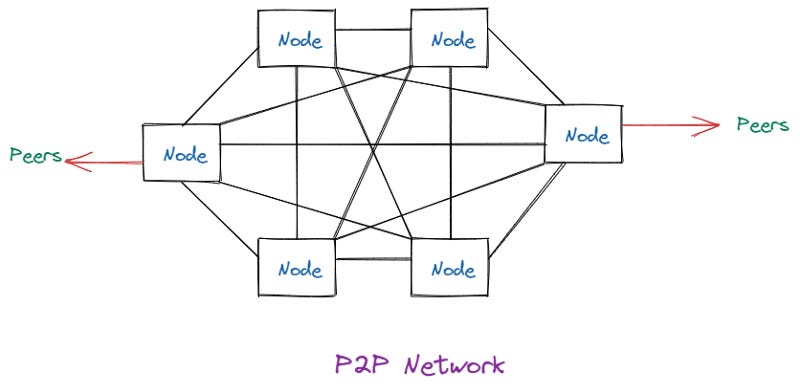
What is a peer-to-peer (P2P) network and how does it work in the blockchain?
A peer-to-peer (P2P) network is a type of computer network in which computers (called “peers”) are connected to each other directly, rather than through a central server. In a P2P network, each peer is able to act as both a client and a server, allowing them to communicate and share data with each other directly.
P2P networks are decentralized, which means that there is no central authority controlling the network. Instead, the peers are able to communicate and coordinate with each other directly.
P2P networks are used in a variety of applications, including file sharing and online communication. They are also an important component of the blockchain, where they are used to facilitate the decentralized nature of the network.
In the context of the blockchain, P2P networks are used to facilitate the communication and coordination between the various nodes on the network. When a new transaction is broadcast to the network, it is received by the nodes and passed along to other nodes until it reaches all of the nodes on the network.
The nodes then validate the transaction and add it to the blockchain, following the rules of the particular blockchain. The P2P network ensures that all of the nodes on the network have a copy of the blockchain and are able to reach consensus on the current state of the network.
What is a public key and a private key and how are they used in the blockchain?
In the context of the blockchain, a public key is a unique identifier that is associated with a user’s wallet. It is a long string of letters and numbers that is generated using a cryptographic algorithm. The public key can be shared with others, and it is used to identify the wallet and receive transactions.
A private key is a secret code that is also associated with a user’s wallet. It is used to sign transactions and provide proof of ownership. The private key must be kept secret at all times, as anyone who has access to it can use it to sign transactions and access the funds in the wallet.
Here’s how public and private keys are used in the blockchain:
A user creates a wallet and generates a pair of public and private keys.
The user shares the public key with others, so that they can send transactions to the wallet.
When the user wants to send a transaction, they use their private key to sign the transaction and provide proof of ownership.
The signed transaction is broadcast to the network, where it is validated by mining nodes.
If the transaction is valid, it is added to the blockchain and the funds are transferred to the recipient’s wallet.
Public and private keys are an important part of the blockchain, as they provide a secure way to identify users and transfer assets. They help to ensure the integrity of the blockchain and prevent fraudulent transactions.
What is a digital wallet and how is it used in the blockchain?
A digital wallet is a software program that stores your digital currency and allows you to send and receive digital currency, as well as track your balance. Digital wallets can be used to store a variety of different types of digital currency, including cryptocurrencies like Bitcoin and Ethereum.
In the context of the blockchain, digital wallets are used to hold your digital currency and manage your transactions. In general, digital wallets use public key cryptography to secure the wallet and the transactions it conducts. A user’s public key is used to create a digital address that can be shared with others in order to receive payments, while the private key is used to sign transactions and prove ownership of the funds associated with the digital address.
Here’s how a digital wallet might be used in the context of the blockchain:
You download a digital wallet onto your computer or phone.
The wallet generates a unique address for you.
You can use this address to receive digital currency from other users. For example, someone might send you 1 bitcoin by sending it to your wallet address.
You can also use your digital wallet to send digital currency to other users. For example, you might send 0.5 bitcoin to a friend by sending it from your wallet to their wallet address.
You can check your balance by looking up your wallet address on the blockchain.
Digital wallets are a convenient and secure way to manage your digital currency, and they are an essential part of using the blockchain.
Here is a list of five popular digital wallets:
Coinbase Wallet: a cryptocurrency wallet and dApp browser developed by Coinbase.
MyEtherWallet: a client-side interface for generating Ethereum wallets and interacting with the Ethereum blockchain.
MetaMask: a browser extension that allows users to manage their Ethereum accounts and interact with dApps.
Ledger Nano: a hardware wallet that allows users to securely store their cryptocurrencies offline.
Trezor: another hardware wallet that supports a variety of cryptocurrencies.
What is a cryptocurrency and how is it used in the blockchain?
A cryptocurrency is a digital asset that uses cryptography for security and is used as a medium of exchange. Cryptocurrencies are decentralized systems that allow for the secure transfer of assets between parties, without the need for a central authority.
One of the key features of cryptocurrencies is that they use a distributed ledger, known as a blockchain, to record transactions. A blockchain is a database that is shared and maintained by a network of computers. Each block in the chain contains a record of multiple transactions, and once a block is added to the chain, it cannot be altered.
Here’s how cryptocurrency is used in the context of a blockchain:
A user initiates a transaction by sending a request to transfer a certain amount of cryptocurrency to another user.
The request is broadcast to the network and is received by mining nodes.
The mining nodes validate the transaction to make sure it is valid and follows the rules of the system.
Once the transaction has been validated, it is combined with other transactions to create a new block of data.
The mining nodes compete to produce a valid hash for the block, using a process called “mining.”
Once a valid hash is produced, the block is added to the blockchain and the transaction is complete.
Cryptocurrencies can be used for a wide range of applications, such as peer-to-peer payments, online shopping, and fundraising. They offer a secure and transparent way to transfer value, without the need for intermediaries.
There are many different forms of cryptocurrencies, also known as digital or virtual currencies. Some of the most well-known cryptocurrencies include Bitcoin, Ethereum, Litecoin, and Monero. These currencies use decentralized control and cryptography to secure their transactions and to verify the transfer of assets. Other types of cryptocurrencies include altcoins, which are alternative versions of Bitcoin that were created to improve upon certain aspects of the original cryptocurrency or to address specific issues or use cases. There are also stablecoins, which are cryptocurrencies that are pegged to a stable asset, such as the US dollar, in order to reduce the price volatility that is commonly associated with cryptocurrencies.
What is a decentralized finance (DeFi) platform and how does it work?
DeFi is a term used to describe financial applications that are built on top of blockchain technology. This means that instead of being controlled by a single entity, like a bank, these applications are open-source and operate on a decentralized network.
One of the main benefits of DeFi is that it allows for greater financial inclusion, since anyone with an internet connection can access these platforms. Additionally, because they are built on blockchain technology, DeFi platforms are often more transparent and secure than traditional financial systems.
So, how does DeFi work? Well, it really depends on the specific application or platform that you’re using. Some common DeFi applications include lending and borrowing platforms, stablecoins, and decentralized exchanges (DEXs).
On a lending and borrowing platform, users can lend out their digital assets to other users in exchange for interest. This can be a great way for people to earn passive income on their cryptocurrency holdings.
Stablecoins are digital assets that are pegged to the value of a real-world asset, such as the US dollar. This makes them less volatile than other cryptocurrencies, which can be useful for people who want to use crypto for day-to-day transactions or as a store of value.
Finally, DEXs are decentralized exchanges that allow users to buy and sell digital assets directly with one another, without the need for a central authority. This can make them faster, cheaper, and more secure than traditional exchanges.
What is a non-fungible token (NFT) and how is it used in the blockchain?
Non-fungible tokens, or NFTs, are digital assets that are unique and cannot be exchanged for something else of equal value. They are often used to represent ownership of things like art, music, and other collectibles.
NFTs are stored on the blockchain, which is a decentralized network of computers that keeps track of transactions and data. This means that the ownership and authenticity of an NFT can be verified and tracked in a transparent and secure way.
One way NFTs are used is in the world of art and collectibles. For example, an artist could create a digital artwork and sell it as an NFT, allowing the buyer to prove they own the original piece and not just a copy. This can help artists protect their work and monetize it in a way that was not previously possible.
NFTs are also being used in the gaming industry, where they can represent in-game items or virtual real estate. For example, a player might own an NFT that represents a rare sword in a video game, which they can then use or trade with other players.
Here are five NFT projects that have gained significant attention in the community:
Cryptovoxels: a virtual world where users can buy, sell, and build on virtual land.
Decentraland: a decentralized virtual world that is built on the Ethereum blockchain.
Axie Infinity: a game that allows players to collect, breed, and battle fantasy creatures called Axies.
CryptoKitties: a game that allows users to collect, breed, and trade virtual cats.
CryptoCollectibles: a platform that allows users to buy, sell, and trade unique digital collectibles.
Ape World: A decentralized virtual world that allows users to collect, breed, and trade virtual apes as non-fungible tokens.
Here I list 5 popular platforms you can exchange NFTs:
OpenSea: A decentralized marketplace for buying, selling, and trading non-fungible tokens and collectibles.
Rarible: A decentralized marketplace for buying, selling, and trading unique digital assets such as art, music, and collectibles as non-fungible tokens.
SuperRare: A decentralized marketplace for buying, selling, and trading unique digital art as non-fungible tokens.
KnownOrigin: A decentralized marketplace for buying, selling, and trading digital art as non-fungible tokens.
Foundation: A decentralized marketplace for buying, selling, and trading digital art and collectibles as non-fungible tokens.
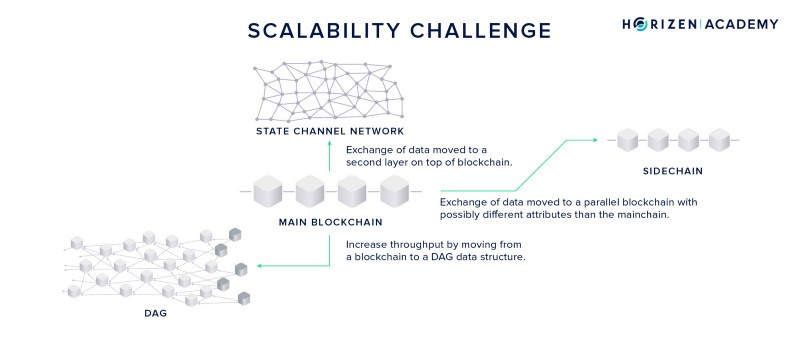
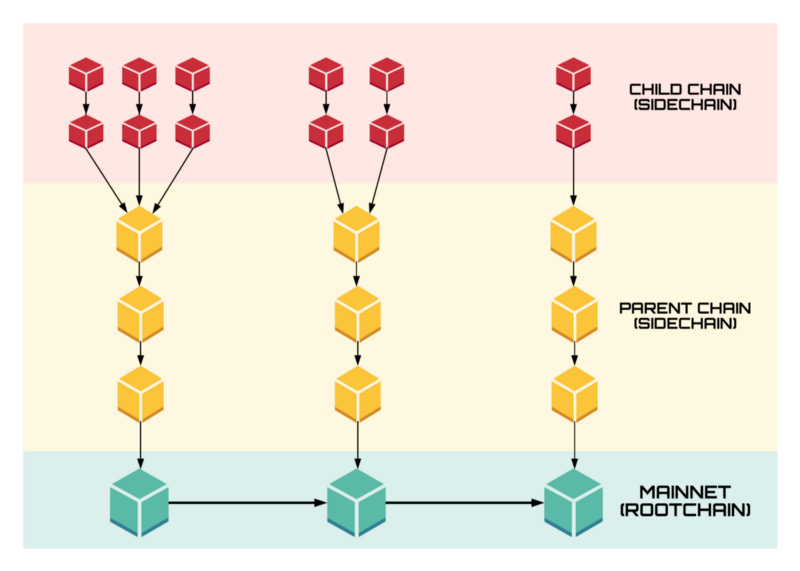
What is a sidechain and how is it used in the blockchain?
A sidechain is essentially a separate blockchain that is connected to a main blockchain (like the Bitcoin or Ethereum blockchain). It allows for assets to be transferred between the main chain and the sidechain, without having to go through the process of being sold and repurchased on the main chain.
So let’s say you have some Bitcoins on the main chain, and you want to use them on a new decentralized application (DApp) that uses its own custom cryptocurrency. Instead of selling your Bitcoins and using the proceeds to buy the new DApp’s cryptocurrency, you can simply transfer your Bitcoins to the sidechain, where they will be converted into the DApp’s cryptocurrency. This is faster and more efficient than going through the process of selling and buying on the main chain.
Sidechains are also useful for experimentation and testing new features or technologies. Since they are separate from the main chain, they can be used to try out new ideas without affecting the security and stability of the main chain.
Overall, sidechains are a useful tool for increasing the flexibility and scalability of a blockchain system. They allow for assets to be easily transferred between different blockchains and can be used for testing and experimentation.
What is a state channel and how is it used in the blockchain?
A state channel is a way to conduct transactions on the blockchain without actually having to broadcast every single one to the entire network. Think of it like a private chat room between two parties where they can conduct multiple transactions without clogging up the main blockchain.
Here’s how it works: let’s say Alice and Bob want to conduct a series of transactions with each other. Instead of sending each one individually to the blockchain, they open up a state channel. This is essentially a virtual channel that only Alice and Bob can access and conduct transactions within. They can send as many transactions as they want within this channel, and once they’re done, they can close it and the final state of their transactions is recorded on the blockchain.
This is useful for a few reasons. First, it reduces the workload on the blockchain itself. If Alice and Bob were to conduct all their transactions individually, it would require a lot of processing power and resources to verify and record each one. By using a state channel, they can conduct multiple transactions without putting any extra strain on the blockchain.
Second, it can also speed up the process of conducting transactions. Instead of waiting for each transaction to be verified and recorded on the blockchain, Alice and Bob can conduct their transactions much faster within the state channel.
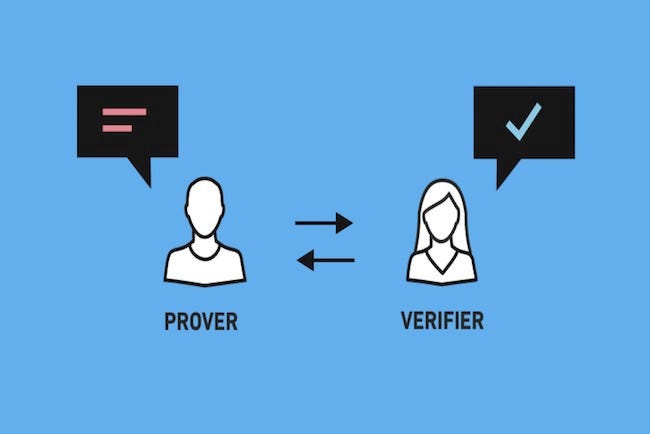
What is a zero-knowledge proof and how is it used in the blockchain?
A zero-knowledge proof is a type of cryptographic proof that allows one party (called the prover) to prove to another party (called the verifier) that they know a certain piece of information without actually revealing what that information is. This is achieved through a series of complex mathematical calculations and protocols that allow the prover to demonstrate their knowledge without actually sharing it.
One of the main uses of zero-knowledge proofs in the blockchain is to enable privacy and anonymity. For example, in a blockchain transaction, the prover (the sender of the transaction) can use a zero-knowledge proof to prove that they have the necessary funds to complete the transaction without revealing their actual balance or any othr personal information.
Another use of zero-knowledge proofs in the blockchain is to enable more efficient and secure verification of transactions. For instance, in a decentralized network, all nodes need to validate transactions before they are added to the blockchain. Using zero-knowledge proofs, the prover (the node proposing the transaction) can prove that the transaction is valid without revealing the actual details of the transaction, which helps to protect the privacy of the parties involved and reduces the risk of fraud or tampering.
Here is another example of a zero-knowledge proof, with more details:
Imagine that Alice is trying to prove to Bob that she knows the solution to a puzzle, without revealing the solution itself. The puzzle is as follows:
“Find a number X such that X multiplied by itself equals 456.”
The solution to this puzzle is X = 21.
Here’s how Alice can provide a zero-knowledge proof to Bob:
Alice selects a random number, let’s say 87, and sends it to Bob.
Bob sends Alice a challenge — a problem that only someone who knows the solution to the puzzle would be able to solve. The challenge might be something like “Multiply your number X by itself, and then add 87 to the result.”
Alice performs the computation using the random number 87 and the puzzle solution (X = 21), and gets the result 478. She sends this result back to Bob.
Bob checks that the result is correct by verifying that 478 minus 87 is equal to 456. This serves as proof that Alice knows the solution to the puzzle (X = 21), without revealing the actual solution.
This is an example of a zero-knowledge proof, because Alice is able to prove that she knows the solution to the puzzle, without revealing what the solution is.
Overall, zero-knowledge proofs are an important tool for ensuring privacy and security in the blockchain, and they are used in a variety of different applications and protocols within the blockchain ecosystem.
What is a plasma chain and how does it work?
A plasma chain is essentially a layer on top of a blockchain, which is designed to allow for faster and cheaper transactions. It works by allowing users to create “side chains” off of the main chain, where they can conduct transactions and move assets around.
The key advantage of a plasma chain is that it allows for much higher transaction speeds and lower fees, as it is not bogged down by the same level of security measures as the main chain. This makes it ideal for situations where speed is more important than absolute security, such as when trading or exchanging assets.
A plasma chain works by adding an extra layer on top of this basic blockchain structure. This layer is known as the “plasma” layer, and it allows users to create side chains that are connected to the main chain. These side chains are essentially miniature blockchains that are only used for specific transactions or activities.
So, let’s say you want to buy a new car using your plasma chain. You would create a side chain on the plasma layer and conduct the transaction there, rather than on the main chain. This would allow you to complete the transaction much faster and at a lower cost, as the security measures on the main chain are not needed.
Overall, a plasma chain is a great solution for situations where speed and efficiency are more important than absolute security. It allows users to conduct transactions and move assets around much faster and cheaper than they could on a traditional blockchain.
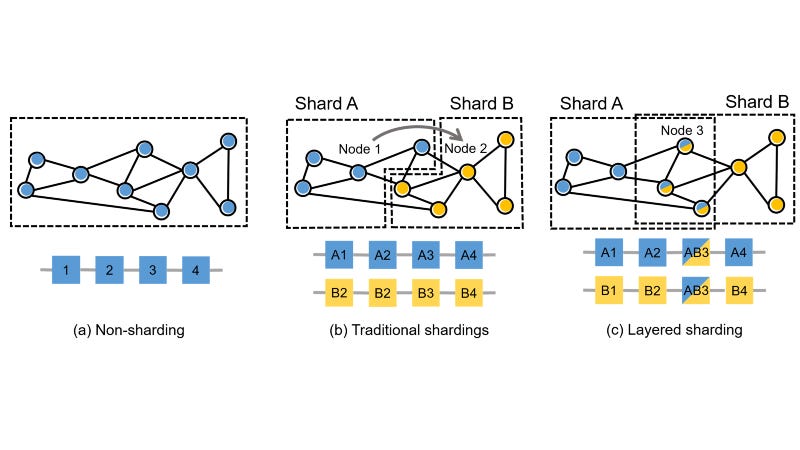
What is sharding and how is it used in the blockchain?
Sharding is a way of horizontally scaling databases by dividing them into smaller, faster, and more easily managed parts called “shards.” In the context of blockchain, sharding refers to a method of horizontally scaling the processing of transactions across multiple nodes in a network.
Here’s how it works:
Imagine you have a large blockchain network with thousands of nodes. Every time a new transaction is made, all of these nodes need to validate it and add it to the chain. This can be slow and resource-intensive, especially if the network is experiencing a high volume of transactions.
With sharding, the network is divided into smaller groups of nodes, or “shards,” each of which is responsible for processing a subset of the transactions. This allows the network to process many more transactions in parallel, increasing its overall speed and scalability.
Sharding is still an experimental technology in the blockchain space, and there are ongoing debates about its pros and cons. Some people believe that it could be a key solution to the scalability problems faced by many blockchain networks, while others are concerned about the potential security risks it may introduce.
Overall, sharding is an exciting development in the world of blockchain, and it will be interesting to see how it evolves in the coming years.
What is a decentralized autonomous organization (DAO) and how does it work?
A decentralized autonomous organization (DAO) is a type of organization that is run using smart contracts on a blockchain. It is called “decentralized” because it is not controlled by any single person or group, but rather by all of the people who participate in it. It is called “autonomous” because it can operate independently, using the rules that are coded into the smart contracts to make decisions.
Here’s how a DAO works:
A group of people come together and decide to create a DAO to achieve a specific goal or set of goals.
They design a set of smart contracts that will govern the DAO, including rules for how decisions are made, how funds are raised and spent, and how new members can join.
The smart contracts are deployed on a blockchain, such as Ethereum.
Members of the DAO can then participate by buying tokens that represent ownership in the DAO.
The DAO operates using the rules that are coded into the smart contracts. Decisions are made through voting, with each member getting a certain number of votes based on the number of tokens they hold.
The DAO can earn money through various means, such as by providing a service or by investing in projects. The profits are then distributed to the members based on their ownership stake in the DAO.
That’s the basic idea! DAOs are still a relatively new concept and there are many different ways that they can be designed and used. Some people see them as a way to create more democratic and transparent organizations, while others are excited about the potential for DAOs to disrupt traditional business models.
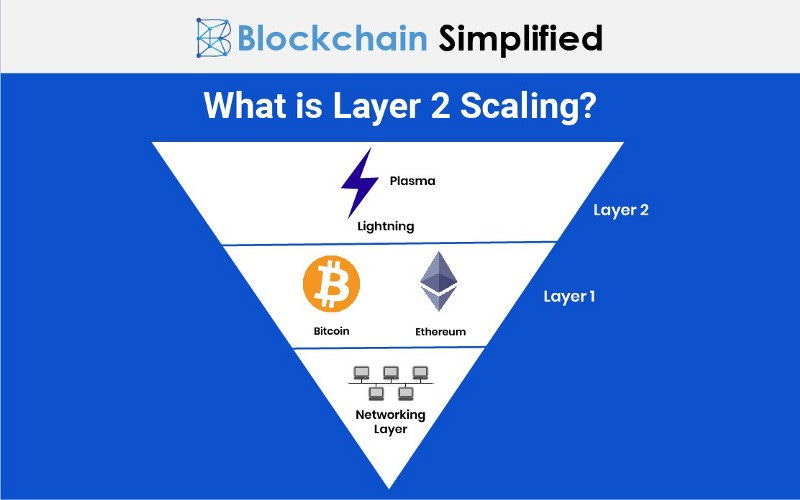
What is a layer 2 solution and how does it work in the blockchain?
A layer 2 solution is essentially an additional layer on top of a blockchain that aims to improve scalability and speed. It works by allowing transactions to be processed off the main chain, and then later verified and added to the main chain in a batch.
Imagine a highway with cars representing transactions. A layer 2 solution would be like a side road that allows some of the cars to bypass the main highway and travel to their destination faster. Once they reach their destination, they are checked to make sure they followed all the rules (i.e. were valid transactions) and then added to the main highway. This helps to alleviate congestion on the main highway, allowing for faster and more efficient processing of transactions.
There are several different types of layer 2 solutions, including the Lightning Network for Bitcoin and Plasma for Ethereum. Each one has its own unique set of rules and protocols, but they all serve the same general purpose of improving scalability and speed.
So in summary, a layer 2 solution is an extra layer on top of a blockchain that helps to improve scalability and speed by allowing transactions to be processed off the main chain and then verified and added in a batch.
What is a proof-of-stake (PoS) consensus algorithm and how does it differ from proof-of-work (PoW)?
A proof-of-stake (PoS) consensus algorithm is a way that blockchain networks can come to a consensus on the state of their ledger without the need for expensive and energy-intensive mining. In a PoS system, the network participants (also known as “validators”) put up a stake of their own cryptocurrency as collateral, and are then chosen to create the next block in the chain based on the size of their stake.
The main difference between PoS and proof-of-work (PoW) is that in a PoW system, miners compete to solve complex mathematical puzzles in order to create new blocks and earn rewards. This process is known as “mining” and requires a lot of computational power and electricity. On the other hand, in a PoS system, the validators are simply chosen based on the size of their stake, which means that the process is much more energy efficient and doesn’t require as much computational power.
Another key difference is that in a PoW system, anyone can participate in the mining process by purchasing specialized hardware and joining a mining pool. In a PoS system, however, only those with a significant amount of the cryptocurrency are able to become validators. This means that PoS systems tend to be more centralized and controlled by a smaller group of individuals or organizations.
Overall, both PoS and PoW are valid ways of reaching consensus on a blockchain, but PoS systems tend to be more energy efficient and less decentralized compared to PoW systems.